New security feature: The deletion notification
Created on 17. March 2023, 12:30 | Category: Info
Dear Posteo customers,
Perhaps you have already noticed that we have released a new feature: the deletion notification. The new security feature protects you from unnoticed data loss; for example, if you have accidentally deleted emails from your account. The new feature has proven to be successful in everyday use. That’s why we would now like to officially present the deletion notification in our blog.
#more#
It is not so uncommon for customers to accidentally delete emails or an entire folder. We would like to provide you with the best possible protection for such cases: Posteo has always offered a special service of creating daily security backups of all email accounts and storing them 7 days for you. If needed, we can then restore these backups for you free of charge.
We have developed the new deletion notification because on a daily basis it was sometimes not satisfactory for us when customers would notice too late – after more than 7 days – that they – or the programs and devices they use – accidentally deleted many emails. We were then no longer able to help them.
With the new deletion notification, this no longer happens. Our system automatically sends a notification via email as soon as the amount of emails in your account is reduced by at least 50 emails within the past 24 hours.
And we can already say that the new feature is a complete success. Meanwhile, almost all customers that accidentally deleted emails contact us in time so that we can restore their data from our security backups. We have been happy to see the positive and relieved responses – thank you for this.
Unlocked cell phones, errors in local clients
The main reasons for accidentally deleting emails can be quickly listed:
Often customers report of “cleaning” gone wrong in their own account – or from smartphones that were not locked in a pocket or bag.
Deletions are more likely to go unnoticed when customers are unaware of deletion settings in their local email clients – such as in Apple Mail, Outlook or Thunderbird. Therefore, it’s generally worth it to check the deletion settings in external email programs. Also, when updating these email clients, errors can sometimes occur that cause emails to be deleted unexpectedly.
By the way, out of principle Posteo never deletes emails from your email account – not even if your storage quota has been filled. We often receive this question.
I received a deletion notification – what do I do now?
If you receive a deletion notification from us in the future, follow these steps:
If you intentionally deleted the emails, simply ignore the deletion notification.
If the messages were accidentally deleted, verify if apps or email clients on your devices are automatically deleting emails. Perhaps your email client (e.g. Apple Mail) automatically emptied the trash. This is sometimes set by default in some email clients. You can, however, change this setting retroactively if you do not want emails to be automatically deleted. For example, also check individual folders, such as the “Sent” folder or your archive.
We do not have any information whatsoever regarding which emails were specifically deleted. The deletion notification has been implemented in a privacy-friendly manner and is entirely generated from values when calculating storage space. We do not look into email accounts and we also do not log which emails were deleted.
Should you be missing emails that you still need and do not have your own backup, please request for us to restore a backup within the next 7 days. This can be done in your settings via “Restore emails”. The backup contains all of the data in your account before the time of deletion. Alternatively, you can request to restore a backup from our customer service via email.
If needed, you can also adjust the deletion settings in your external email client to prevent unwanted deletions in the future.
Adjusting or deactivating deletion notices
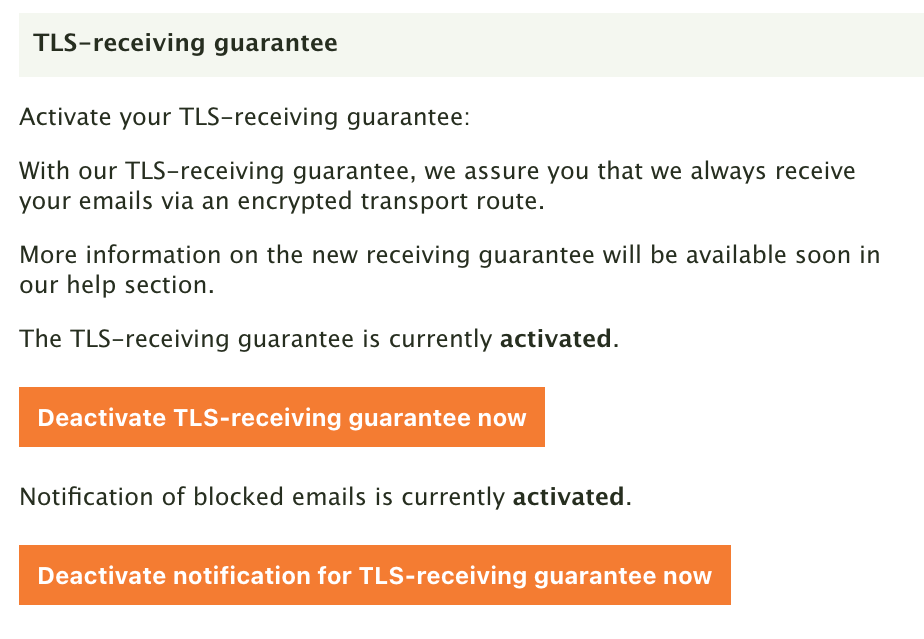
Another tip: You can specify in your settings via “Password and security” to receive a notification only when more emails are deleted. This setting is particularly useful for people who regularly delete a lot of emails. If you no longer wish to receive deletion notifications, you can also deactivate the feature there.
We also recommend regularly creating your own backups of all saved data.
Best regards,
Your Posteo Team